Depending on your level of knowledge about the specifics of website development, the process can seem like a black box. Having a good working knowledge of the parts involved can save your company from ending up in a situation, months or years down the road, where you find out you don’t have access to or even ownership of certain parts of your website or data. In this edition of Plain Talk, we’ll go over the most important facets of website ownership and give you an outline of items you absolutely must have control over to ensure your company’s website is completely under your control.
The items we’ll go over are:
Internet Domain Ownership
Domain ownership is the process of acquiring a domain name for a website. The domain name is the address of a website on the internet (for example, priceweber.com). Domains are purchased from a domain registrar. The registrar is the entity that sells internet domains and registers them in an appropriate second-level domain name registry.
When someone purchases a domain, they decide who the actual owner is, who the contacts for the domain are, how long it’s registered for and whether it automatically renews itself at the end of the paid registration period.
This process not only allows the purchase of the domain name but also provides the necessary network connections required to associate the name with network addresses that are kind of like the phone numbers of the servers responsible for hosting the website, e-mail servers and more.
Nothing else matters as much as ownership of this initial property. If the person, agency or online service offers to register your domain for you, then THEY might actually have ownership of the domain or have sole access to its details. Your domain should always be registered in your company name by a trusted member of your organization.
Hosting
A host is a website’s home on the internet. It is where all the web pages, data and other content are stored. Hosting a website can be done on a physical server inside your company’s office network or some other facility that houses the server and provides connectivity to and from it to the internet. Depending on your company’s IT infrastructure, hosting can also be provided on a virtual server that exists in the cloud. In recent years it has become far more cost-effective for most companies to choose cloud hosting because of the flexibility in scaling the computing resources and low upfront investment.
With all that said, your company may have neither of the above options in place, and when you hire someone to build your website, they may offer to host the website “for you” on their server or cloud environment. The thing to watch out for here is to make the choice where your company has control at the account ownership level.
A Little Information About Cloud Hosts
There are different types of hosting accounts: most notably shared and dedicated. Shared hosting accounts are cheaper, but they don’t offer as much control over your website, so you might not be able to make changes to it or upload new content as quickly. A shared hosting account is also, as the name implies, shared with companies on the same server, which can lead to problems if one or more of the sites sharing the host’s resources is very busy or has an issue that can affect the performance of the other sites on the server. Dedicated hosting accounts are more expensive, but they give you more control over your website and speed up access to it. Some of the main factors in choosing a cloud hosting provider are security, reliability, pricing and performance.
The Programming Code
Code can be delivered in two main ways: non-proprietary (uncompiled) and proprietary (compiled). Both will run your website, but only uncompiled code is completely editable if you need to change something about it later.
Non-proprietary code is a set of instructions that can be executed on any similar type of computer, regardless of the specific setup of the hardware or operating system. The two most common types of operating system stacks are the Microsoft OS and the Linux OS. Most website programming code is created to run on one or the other of those two stacks. In the general sense, all you should need to know about your website code compatibility is which of these two stacks it runs on, and you can choose from a myriad of places to host it. Non-proprietary code provided to your company for either scenario ensures your website is portable to another host should the need arise.
In contrast to this, there is proprietary “compiled code,” which refers to a computer program that has been translated from its original human-readable programming language into a machine-specific language. Think zeros and ones. This translation process, called compilation, produces an executable program that will run on the intended host but cannot be changed easily or even at all in some cases.
The main disadvantage of compiled code is that it cannot be changed once it has been compiled into machine-specific instructions. Uncompiled code can be changed because there are no limitations on what can be done with it as long as the programmer knows how to do so. You should always make sure that the company or individual programming your website contractually agrees to provide you with the full uncompiled code should you ask for it.
Access
Even if you own the hosting contract for your web server, you will most likely appoint individuals who are building your website with the ability to create and adjust access methods to the host server. The ssh and sftp protocols are two of the most popular protocols for remote logins. They are often used to connect to a server or a remote computer system. They are used for file transfer and can be used for other purposes as well. Similar protocols are used for database access and, in some enterprise cases, for access to a network security device in front of the web host.
If possible, you want your company to own and control the highest level of access to your server, database and security devices. These are typically set up when you acquire the contract for a host or virtual server. The highest level of access is often referred to as “root” access. An administrator with root access can do anything and everything to a server, so it should only be shared with trusted employees and partners. The best practice is to use the root account to create other user accounts for ssh, sftp, etc., which have the needed level of access to be given to the people or company working on your website, but that don’t have the power to remove your root access to the server.
The same principle applies to a CMS (Content Management System) but with less ability to retain a type of “root” control. You should state in your agreement with your website builder that a user account within the CMS software will be given to you, which has the highest level of control over the configuration of the CMS.
Security Controls
There are certain items involved in the security of your website that you need to make sure you understand and have ownership of. In this article, we won’t go into some of the enterprise-level security options, such as web application firewalls, because they are less common to need to manage at a granular level. We’ll focus on the common elements that you need to keep your site running securely.
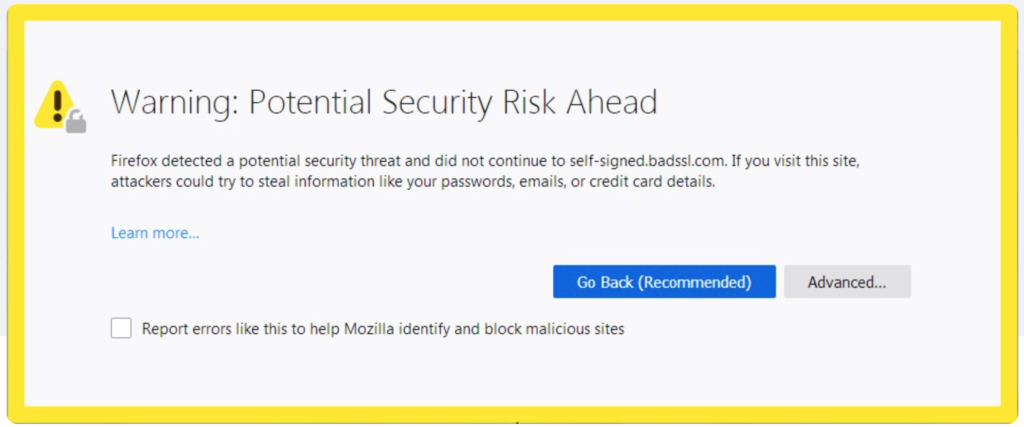
SSL security certificates are one of the most important tools for online security. They are used to encrypt data that is sent between a web server and a browser, ensuring that it is not read by any third party. They also help in verifying the identity of the person on the other end of the connection. Having an SSL certificate that is NOT current and valid causes your site to be flagged by browsers and search engines and will greatly deter your visitors from being able to access your website. Therefore, it’s important to have ownership of the certificate and the process for deploying it to your web host. Both of these come standard with a good Cloud Hosting Service Provider.
An SSL certificate has a lifespan. The lifespan of an SSL certificate depends on various factors, such as:
- How often it is used
- The type of certificate
- The level of security it provides
- Whether it has been revoked or compromised
Other security factors to make sure your company has the highest level of control over are the authentication methods and administrator user account review process.
Many companies use a single-sign-on (SSO) and/or a two-factor authentication process for their websites and apps. SSO means that users can provide the same password they use for another company system to access the website. Two-factor authentication means that users need to provide two separate pieces of information to access their accounts, such as a password and a code that is sent to the user’s phone. Both of these options require the use of third-party software that is important for your company to own the contract for and the highest level of control of. Not having control of either of these could make your website inaccessible until someone can disable these features.
Your company should regularly review who has administrator-level access to the server and to the CMS for your website. They should also review who has access to the website’s code and configuration files. Some of these people may not need this level of access, so they can be removed from the list. Your company should also periodically review all other accounts that have any type of level access to the server, database or CMS and make sure that they still need it or if their privilege levels can be lowered or removed.
Another aspect of website security that your company should have in place and have ownership of is basic vulnerability scanning to monitor for malware that can damage your site’s reputation or cause a data breach. Malware is a type of software that is designed to cause problems with or damage to a computer system. Malware can be classified into different categories, such as viruses, worms, trojan horses, ransomware and spyware.
Website malware scanning is the process of scanning websites for malware and other security risks. The purpose of website malware scanning is to identify any potential threats that may exist on the website. Website owners should use this process to make sure their website is safe from malicious attacks and threats.
Availability monitoring is another best practice that identifies an outage of your website caused by hosting issues or code errors. Many website administrators believe that if they don’t see any errors in their logs, then everything is alright. However, this is not the case. Errors can happen without being visible in the logs and without being detected by the administrator.
In order to avoid this problem, it’s important to keep an eye on your server and make sure that there are no issues. One way of doing this is by using a monitoring service.
Analytics
Last but not least is analytics. This is most commonly accomplished by integrating Google Analytics into your website from an administrator’s Google account. Google Analytics (GA) is a free web analytics service offered by Google that generates detailed statistics about the visits and traffic to websites. This can be done through the Google Control Panel.
The Google Analytics account owner has full control over which data is collected and how it is analyzed, as well as the ability to grant access to other users who share and configure the analytics data. Your company should own the parent account for Google Analytics so that in the event you change developers or move your hosting, there is contiguous information being fed into your analytics master account.
Also, be certain your site has GA4. GA3, commonly referred to as Universal Analytics (UA), is going away on July 1, 2023, as Google phases out the support of 3rd party cookies. GA3 uses measurements based on sessions and pageviews. GA4 instead uses a measurement model based on events and parameters. We discuss this more in B2B Digital Marketing Today – Three Critical Things You Need to Know.
What next?
A website is a complicated orchestration of many dependent elements. It’s very important that your company maintains control over the administration and access to those elements as much as possible. What we’ve covered in this article are the main points to consider, but depending on the application, there can be others. It’s essential to choose a website development partner that works with your company to accomplish the things we’ve discussed here with transparency and a contractual agreement to work on your behalf.
At PriceWeber, we pride ourselves on being a trusted partner who empowers our clients to achieve these goals. If you have any questions regarding anything we’ve covered here, feel free to reach out to us for a consult at (502) 499-4209 or drop us a note here, and we’ll be happy to help.